Understanding Stealth Scans XMAS vs FIN
When attackers or penetration testers explore a network, they often rely on stealthy network scanning methods rather than noisy probes. Two of the most discussed techniques are the XMAS scan & FIN scan attacks. Both exploit quirks in TCP/IP stack implementation issues to quietly reveal details about open vs closed ports without raising alarms.
Instead of overwhelming a system, they use crafted packets with unusual TCP flags (FIN, URG, PSH, RST, SYN, ACK). This allows them to bypass weak defenses and test how a host responds. For security teams, detecting these scans early is crucial to stop deeper breaches before they begin.
What is a TCP Xmas Scan?

The Xmas scan is one of the most unusual port scanning methods. In simple terms, it sends packets with multiple TCP flags used in xmas scan (FIN, URG, PUSH) all set at once. Because the packet looks “lit up” with many flags, it earned the Christmas tree scan meaning in networking. This technique is particularly effective against devices with weak tcp/ip stack vulnerability testing methods.
The Nmap XMAS scan is the most famous tool for this type of attack. It can identify whether ports are open vs closed ports or filtered. For defenders, the real problem is that such scans don’t always show up in packet inspection security logs, especially if stateful vs stateless firewalls are poorly configured. This makes detection harder than with a simple SYN scan.
1. How Xmas Scan Works
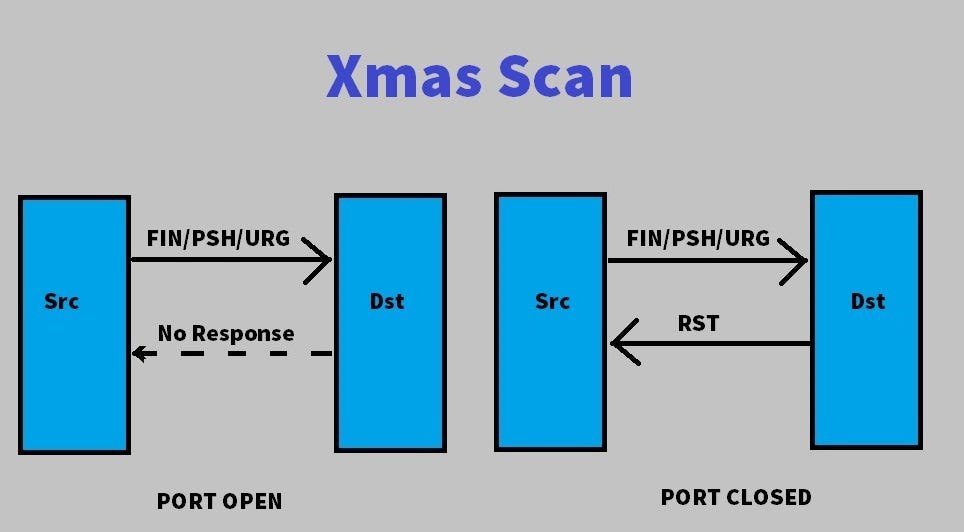
An Xmas scan works by sending packets with FIN, URG, and PSH flags set. If the port is closed, the system replies with a RST flag. If the port is open, many systems—especially those with weak TCP/IP stack implementation issues—ignore the packet. This silence reveals which ports are alive.
2. Why It’s Called “Xmas”
The name comes from the fact that the packet is “lit up” with multiple flags, like a Christmas tree covered in lights. This analogy makes it easier for beginners to remember. But for professionals, it represents one of the cleverest stealth scanning methods in cybersecurity ever created.
3. Common Use Cases in Cyberattacks
Hackers use Xmas scans to discover hidden entry points, bypass poorly configured firewalls, and test for tcp/ip stack vulnerability testing methods. Ethical hackers also use them during penetration testing techniques to ensure networks aren’t exposed to these advanced port scanning techniques. The defensive use of xmas scan for penetration testing is well accepted.
What is a TCP FIN Scan?

A FIN scan is another stealth scanning technique. Instead of using multiple flags, it sets only the FIN flag. When sent to a closed port, the target should reply with a RST. If the port is open, many operating systems simply ignore it. This creates a quiet way to check for open vs closed ports without attracting attention.
The difference between xmas scan and FIN scan lies mainly in the number of flags used. Where Xmas lights up three flags, the FIN scan uses only one. This simplicity makes it even stealthier on some systems, but it also has limitations.
1. How FIN Scan Differs from Xmas Scan
The Xmas scan relies on multiple flags being set. The FIN scan, on the other hand, uses just one. Because of this, it can sometimes bypass intrusion detection systems (IDS) more effectively. But it doesn’t work on all platforms, especially Windows systems which reject such packets differently.
2. Advantages of FIN Scan for Attackers
The main advantage is subtlety. Since it only uses one flag, the packet looks more natural. This helps attackers during malicious network probing. It’s often part of stealthy network scanning methods used to evade packet inspection security tools.
3. Limitations of FIN Scan
A big weakness is its failure against Windows. Many Microsoft stacks respond with RST regardless of port status. This makes FIN scans useless in those cases. Strong stateful firewalls can also block these attempts, reducing their effectiveness.
Key Differences Between Xmas and FIN Scans
Although both are stealth scanning methods in cybersecurity, they aren’t the same. Understanding these differences helps defenders and ethical hackers alike.
1. Packet Flags Comparison
- Xmas Scan: Uses FIN, URG, PSH simultaneously.
- FIN Scan: Uses only the FIN flag.
This explains the christmas tree scan meaning in networking versus the minimalistic approach of FIN scans.
2. Evasion Capabilities
Xmas scans are more visible because of multiple flags. FIN scans, however, are quieter. But both can bypass stateless firewalls while stateful vs stateless firewalls make a big difference in detection.
3. Detection Difficulty
Both scans exploit tcp/ip stack vulnerability testing methods. However, advanced intrusion detection systems vs xmas scan and FIN scans can now identify these probes. The challenge is higher when combined with other port scanning techniques in ethical hacking.
Real-World Impacts of Xmas and FIN Scans
The effect of these scans isn’t just theory. They’re often used in cybersecurity vulnerability scanning against real organizations in the USA. Hackers rely on them to silently map networks before launching ransomware or data theft campaigns. In many cases, businesses never realize they were scanned until the breach happens.
1. Examples of Exploitation
Case studies have shown that attackers used Nmap XMAS scan options to discover filtered ports in network scanning. Once open ports were found, attackers deployed malware. Reports from CERT highlight how attackers exploited tcp/ip stack implementation issues in routers and IoT devices.
2. Risks for Businesses and Organizations
The risks are serious. From regulatory fines to loss of customer trust, the impact of ignoring stealthy network scanning methods is high. Many breaches in the U.S. began with silent malicious network probing.
3. Legal and Ethical Implications
The big question—is xmas scan legal or illegal—depends on intent. Using it on your own network for defensive use of xmas scan for penetration testing is legal. Doing it against others without permission violates laws such as the U.S. CFAA (Computer Fraud and Abuse Act).
Tools Commonly Used for TCP Xmas and FIN Scans
Attackers and defenders alike use certain tools for these scans. Vulnerability assessment tools include a range of options, but a few stand out.
1. Nmap and Its Scanning Options (-sX, -sF, -sN)
The most popular tool for port scanning methods is Nmap. The commands -sX, -sF, and -sN trigger Nmap XMAS scan, FIN scan, and NULL scan. These are classic penetration testing techniques used worldwide.
2. Npcap for Packet Capture against TCP XMAS & FIN Scan
Npcap integrates with Nmap to capture packets at a deep level. It’s essential for Windows-based packet inspection security. Ethical hackers use it to verify tcp/ip stack vulnerability testing methods.
3. Other Security Tools
Wireshark helps visualize packets. Metasploit combines scanning with exploitation. Zeek and Snort act as intrusion detection systems (IDS), monitoring for advanced port scanning techniques.
How to Detect TCP Xmas and FIN Scans

Defenders must be proactive. Detecting XMAS Scan vs FIN Scan Attacks requires layered strategies.
1. IDS/IPS Role (Snort, Suricata, Zeek)
Modern IDS tools can spot unusual flag combinations. Signatures detect Tcp flags used in xmas scan (FIN, URG, PUSH) and raise alerts. IPS systems can block packets instantly.
2. Firewall Logging and Alerts
Logs tell the story. By reviewing traffic, admins can learn how to detect xmas scan with firewall rules. Stateful firewalls do a better job compared to stateless ones.
3. Behavior-based Detection
Instead of only checking signatures, anomaly detection analyzes traffic behavior. This form of cybersecurity vulnerability scanning helps find unusual stealthy network scanning methods.
Defense Strategies Against TCP XMAS & FIN Scan
Knowing about these scans is not enough. Defense must be active and layered.
1. Configuring Firewalls Correctly
Properly configured firewalls can prevent how to protect against xmas scan attacks. Rules should block suspicious port scanning techniques in ethical hacking attempts.
2. Intrusion Prevention Systems (IPS)
IPS solutions not only detect but also block packets. This stops malicious network probing before it reveals information.
3. Network Monitoring Best Practices
Continuous monitoring, alerting, and packet inspection security help protect critical systems. Using vulnerability assessment tools regularly ensures strong defenses.
FAQs on TCP Xmas FIN Scans
1. Are these scans still effective today?
Yes, but less than before. Modern intrusion detection system vs xmas scan strategies are stronger. Yet, they still work against outdated devices.
2. Can defenders use them for ethical testing?
Yes, defensive use of xmas scan for penetration testing is common. It helps find weak tcp/ip stack implementation issues.
3. Which is more dangerous: Xmas or FIN?
Both can be risky. The difference between xmas scan and FIN scan is small in impact but big in technique. When combined with advanced port scanning techniques, they become more powerful.
Stay ahead in the digital world with our latest articles on top tech news and the rise of Blue Artificial Intelligence. From breakthrough innovations to practical insights, we bring you easy-to-read guides that explain how emerging technologies are shaping businesses, security, and everyday life. Whether you’re curious about the future of AI or want to explore the smartest tools in tech, our blog gives you the knowledge you need in simple language.
Conclusion
In today’s cybersecurity landscape, XMAS Scan vs FIN Scan Attacks remain a critical subject. They represent clever stealth scanning methods in cybersecurity that test the limits of tcp/ip stack vulnerability testing methods. By understanding the advantages and disadvantages of xmas scan and FIN scans, defenders gain an edge.
The key takeaway is clear: while attackers use these techniques for malicious network probing, defenders must use them for port scanning techniques in ethical hacking. With strong packet inspection security, effective intrusion detection systems (IDS), and well-configured stateful firewalls, organizations in the USA can stay one step ahead.